In my earlier posts on this topic, I discussed how the Zero Trust security model addresses many of the emerging security challenges caused by SaaS. But let’s get tactical now. What are the critical processes and tools required to implement Zero Trust and achieve effective SaaS management?
Eight steps to implement effective SaaS management and Zero Trust
- Use a centralized access control model. This relies on the core principles of role-based access control with role definitions and governance using identity and access management (IAM) and privilege access management (PAM) products.
- Apply strict access controls to sensitive data, systems, and applications. Only allow access to assets that users need to do their jobs.
- Use context-based authentication also known as Adaptive Access with the ability to step up factors that are required to verify the rightful user who is requesting a service. Factors can be a combination of devices, certificates, keys, login time, geolocation, etc.
- Document and understand the current security architecture. Discover holes and gaps, and develop your future security architecture to plug these holes and gaps.
- Leverage user and entity behavior analytics (UEBA) to look for and alert on abnormal behaviors for a specific user, system, or device, and require step up authentication measures.
- Establish a policy framework for your org and write the rules for it. This should include steps like activation, investigation, remediation, and enforcement of these rules and policies.
- Monitor the network. Inspect and log traffic, and continue to update rules based on your UEBA.
- Remediate and enforce in real time. Get visibility into user activity, apply rule-based dynamic access controls, remediate issues in real time, and enforce these policies either through one-off or bulk actions.
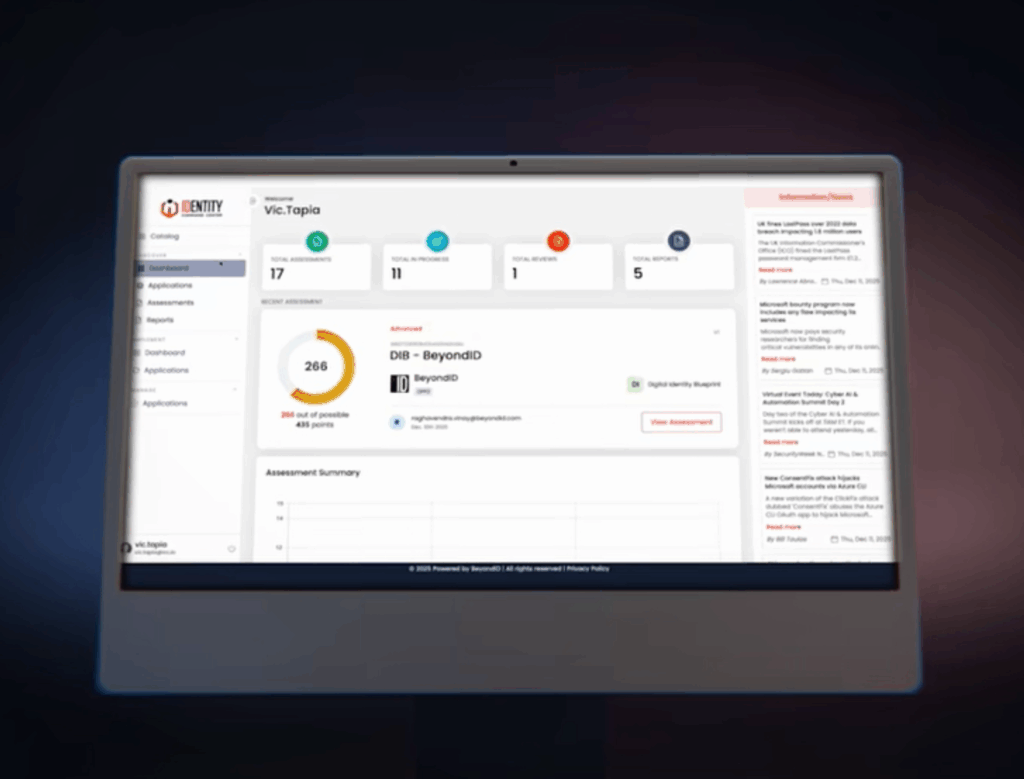
Ten key technologies required to implement effective SaaS management and Zero Trust
- IDaaS for managing workforce and customer user identity, and authentication including user lifecycle management and adaptive/contextual access management.
- SaaS Management Platforms (SMPs) for deeper lifecycle management starting with: Activation : Get better visibility into data and app settingsInvestigation: Uncover policy violations and security vulnerabilities Remediate: Correct violations with one-off or bulk actions Enforcement : Automate multi-step remediation plans across applications.
- IGA for managing identity governance and administration from access requests, access recertification, Segregation of Duties (SoD), and automation of user lifecycle management including compliance controls required by SOX, HIPAA, PCI-DSS, GDPR, FedRAMP, etc.
- PAM to establish a least privilege access model for protecting sensitive data and applications in the cloud or on-premise including operating systems and workloads.
- CASB to establish a gateway and roll out policy orchestrators for using SaaS apps.
- HRIS as the source of truth to implement joiner, mover, and leaver use cases, and to enable real-time provisioning and deprovisioning for users to access authorized applications, data, and systems. This is critical to reducing the attack surface since most data breaches occur because of compromised inside actors.
- SIEM or UEBA solutions to look for and alert on abnormal behaviors.
- ITSM for incident management, release management, people management, and change management.Secure
- Web Gateway to protect remote offices connected directly to the internet and apply next generation firewalls that can protect both cloud and on-premise systems and applications.
- Web and mobile security to protect web and mobile applications in real time from imitation (fraud) attacks. This technology proactively alerts companies when users’ credentials have been compromised.
In conclusion, effective SaaS management leveraging a Zero Trust security model is a journey that requires a thoughtful and comprehensive strategy and architecture. Best implemented in phases with surgical tactics backed by best-in-class technologies and best practices, it should be fully operationalized over a period of time, and constantly optimized on an ongoing basis.
Let’s continue our conversation. I’d love to get your feedback. Feel free to email me at [email protected]