Deliver Lasting Value with Identity
What We Do
Identity today isn't just about access. It's about creating a strategic advantage. We solve complex identity challenges to enable secure total experiences, delivering measurable results with proven success. Our work goes far beyond IT to impact your entire organization and digital ecosystem.

A Secure Total Experience
A secure total experience combines security and an engaging user experience seamlessly across every touchpoint. Unlock the full promise of your digital identity program with our end-to-end identity management services.
Enhance Security
Prevent costly breaches, fraud, and unauthorized access with flexible identity services and 24x7 real-time support.
Optimize Experiences
Deliver safe, frictionless experiences that increase adoption, enhance efficiency, and build trust.
Drive Efficiency
Automate and streamline identity processes to eliminate errors, reduce overhead, and lower costs.
Ensure Compliance
Simplify audits with strong identity controls for HIPAA, GDPR, SOC 2, NIST, and other requirements.
Support Innovation
Accelerate digital transformation with agile access management services that fuel innovation at an enterprise scale.
End-to-End Identity Management Services
From strategy to implementation and 24x7 security operations support, we offer comprehensive, AI-powered access management services to keep you ahead of rapidly evolving challenges and threats.
Advisory Services
Navigate complex identity challenges confidently with expert-led strategy and planning. Our advisory services are built on decades of specialized expertise, deep technical knowledge, and vertical-specific acumen.
Strategy
Create a path for the future that aligns with your organization’s strategic goals, with the expertise and experience of a proven partner.
Roadmaps
Bring your vision to life with a phased plan for modernization, and vendor-agnostic technology recommendations.
Zero Trust
Move from an ad hoc approach to a mature, structured system that improves security, efficiency, and experiences.
Implementation Services
Modernize legacy platforms and integrate identity and access management systems across cloud, hybrid, and on-premise environments. Our seamless integration solutions meet your unique needs.
Design
Integration
Deployment
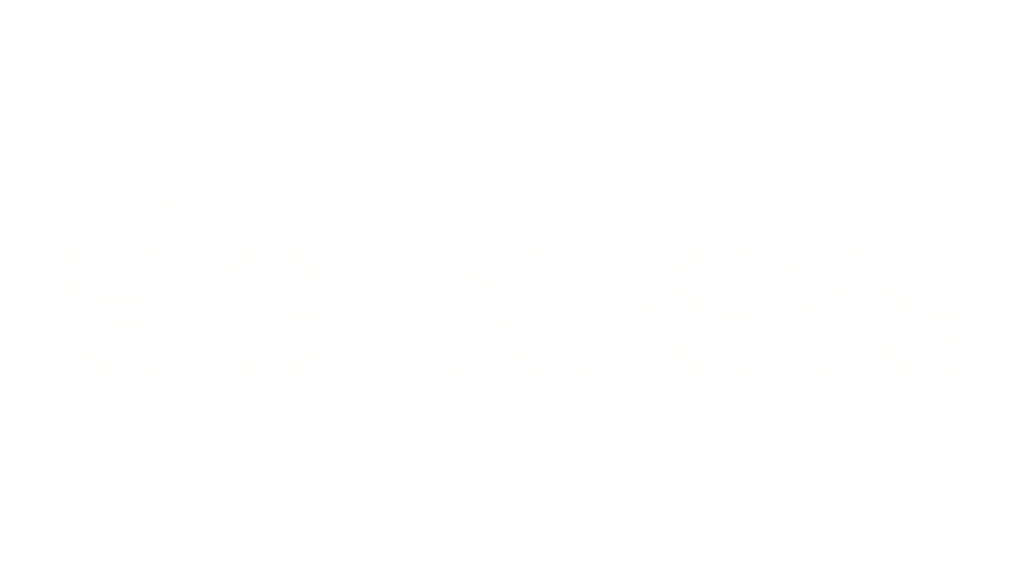
Security Operations and Managed Support
Get 24×7 cybersecurity protection with ongoing real-time support. Our Security Operations Center (SOC) delivers continuous protection and management services.
24x7 Protection
System Management
Managed Support
Your Success Is Our Success
We've helped hundreds of organizations plan, deploy, and manage their identity programs — and we're here to help you too. Learn more about our impact.
Frequently Asked Questions
What level of ongoing support does BeyondID provide?
We are your identity security partner, delivering end-to-end managed identity services tailored to your needs. From strategic advisory to roadmaps, implementation, and 24×7 security operations, we meet you where you are in your journey, accelerating your goals with specialized IAM expertise.
How does BeyondID support compliance requirements?
We simplify audits with strong identity controls for HIPAA, GDPR, SOC 2, NIST, and other requirements. Our comprehensive identity management services reduce complexity, providing identity-first governance and real-time audit support.
What makes BeyondID different from other IAM service providers?
We are wholly focused on identity, delivering strategic advisory, implementation, and 24×7 monitoring and support. We go beyond implementations, providing end-to-end managed services with proven success for hundreds of organizations.
What is the difference between identity management and access management?
Identity management establishes and maintains digital identities throughout their lifecycle, while access management controls what resources those identities can access. BeyondID delivers comprehensive identity and access management services that combine both, ensuring secure, seamless experiences across your entire digital ecosystem.
Ready to Unlock the Full Promise of Identity?
Few cybersecurity firms are wholly focused on identity, providing strategic advisory, implementation, and 24x7 monitoring and support. Discover the difference with BeyondID — your success story starts here.