So, you’re not an identity expert. Companies investing in Identity and Access Management (IAM) usually aren’t. That’s why partnering with a managed identity services provider like BeyondID is an important first step.
On a conceptual level, IAM is quite accessible; the trick is to stay out of the weeds. So if you’ve begun your research into the world of IAM and are trying to steer clear of more technical explanations, consider this analogy: IAM is like a well-run hotel.
The Analogy
Your company’s system (Okta Platform) is a five-star, beachfront hotel. It’s run by a friendly staff of hotel employees (your workforce), and visited by hundreds of traveling guests (your customers) each day. Each employee and guest is issued a keycard that allows them to move about the hotel property within the reasonable limits of their responsibilities and privileges – these rules and boundaries represent our hypothetical implementation of IAM. Similar to how you wouldn’t want uninvited guests getting access to these privileges, IAM cyber security is of utmost importance. That’s why our IAM consulting services implement best practices to keep your identity secure.
Employees
Beachfront hotels don’t run themselves, and the five-star experience takes a village. To ensure each guest enjoys a wonderful stay, hotel employees must have seamless access to the areas, supplies, and information they need to do their job. But for the sake of productivity and security, no keycard should afford more access than a staff member needs to fulfill their individual duties.
In your hotel, the responsibilities of a concierge differ greatly from those of a masseuse, and don’t be surprised if a housekeeper’s keycard opens a few more doors than a snorkel adventure guide’s. Guest services will access visitor profiles in order to put the finishing touches on a memorable stay, but the only staff members authorized to enter guest rooms are the kind who leave towel swans, clean sheets, and pillow chocolates behind. Certain IAM solutions can be tailored to prevent certain customers, employees or departments from having specific access.
Hotel Guests
Personally programmed keycards unlock a seamless stay for hotel guests. With access to every area and amenity associated with their booking, guests decide what their stay looks like. Hotel guests can access the fitness center, reserve a poolside lounge, and even order drinks with a tap of their keycard. Where each keycard touchpoint syncs with a singular guest profile, guests enjoy a continuous experience throughout their stay. In this case, there are IAM programs that can be customized to a user’s identity profile similar to a hotel keycard.
Management
In your hotel, you decide where access is granted, and provisioning and deprovisioning happens at the drop of a hat. When guests check-in, they know access is provisioned immediately, and they can expect it to terminate at the time of checkout. To protect against theft by disgruntled employees, provisioning and deprovisioning for employee keycards is just as instantaneous in instances of hiring and firing. Your team members have access to what they need to do their jobs, but not to what might provide a distraction or potential loss to the business.
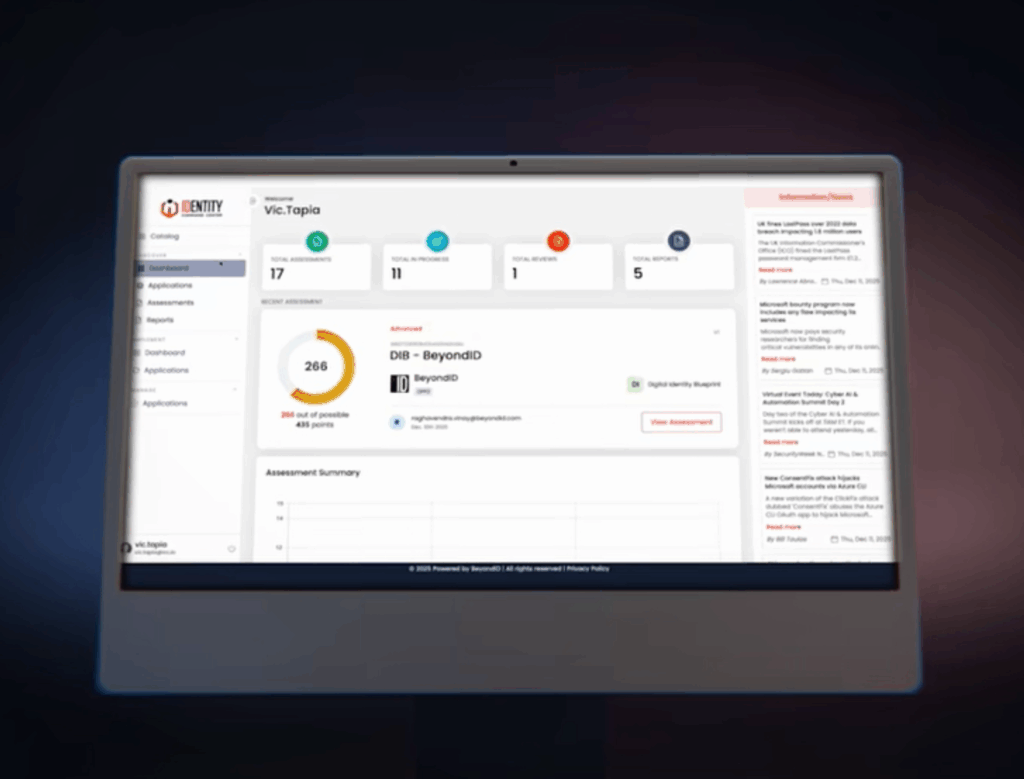
BeyondID’s IAM Solutions
Whether we’re talking about visiting a five-star hotel or interacting with your company’s digital interface, identity is the key to a seamless experience. BeyondID can tailor our IAM technology and solutions to best fit your company’s identity needs. We plan, deploy, and manage SSO to cloud and on-premises applications for cloud access security and consumer identity. To find out how IAM can transform your organization, contact BeyondID today.